Bloklab Blog
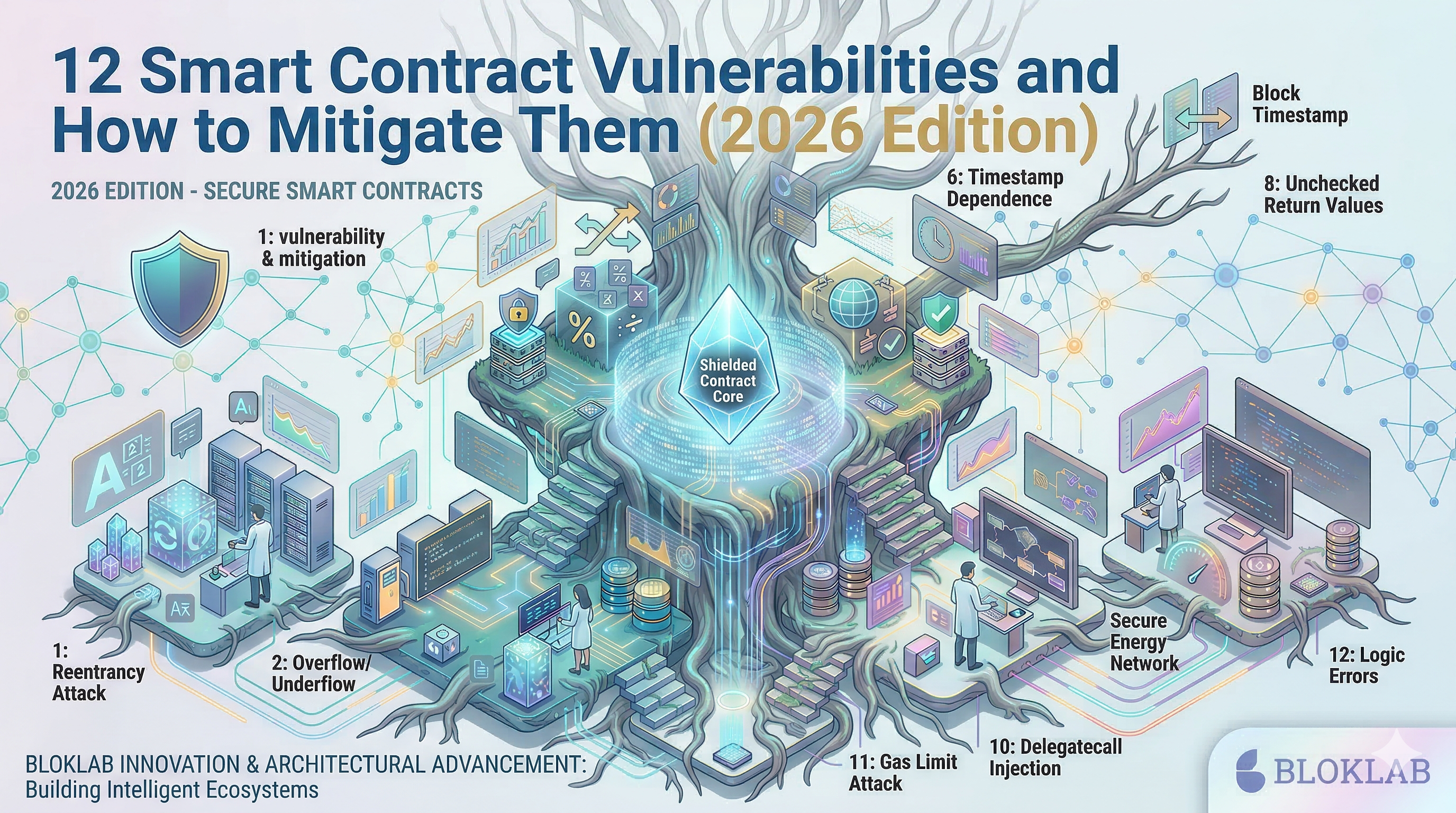
12 Smart Contract Vulnerabilities and How to Mitigate Them (2026 Edition)
Published on 3/18/2026
Smart contract vulnerabilities continue to evolve alongside blockchain adoption. This guide covers 12 critical security risks in 2026 and provides practical mitigation strategies to help developers build resilient, production-grade decentralized applications.
12 Smart Contract Vulnerabilities and How to Mitigate Them (2026 Edition)
Advanced Security Insights for Modern Web3 Systems
As blockchain infrastructure matures, smart contracts have become the backbone of decentralized finance (DeFi), digital identity systems, token economies, and on-chain governance. However, with billions of dollars locked in smart contracts, they remain one of the most attractive attack surfaces in the digital world.
Security in 2026 is no longer just about avoiding basic bugs—it requires a system-level mindset, combining secure coding practices, formal verification, runtime monitoring, and economic design awareness.
This article explores 12 of the most critical smart contract vulnerabilities along with modern mitigation strategies used by leading protocols today.
1. Reentrancy Attacks
The Issue
Reentrancy occurs when a contract calls an external contract before updating its internal state, allowing the external contract to re-enter the original function and manipulate logic.
Impact
Draining of funds
State inconsistency
Protocol collapse
Mitigation
Use Checks-Effects-Interactions pattern
Implement reentrancy guards
Avoid external calls before state updates
2. Integer Overflow and Underflow
The Issue
Arithmetic operations exceed storage limits, causing unexpected wraparounds.
Impact
Token supply manipulation
Incorrect balances
Logic bypass
Mitigation
Use modern Solidity (≥0.8) with built-in overflow checks
Apply safe math libraries where necessary
3. Access Control Vulnerabilities
The Issue
Improper permission management allows unauthorized users to execute privileged functions.
Impact
Unauthorized minting
Contract takeover
Governance manipulation
Mitigation
Use role-based access control (RBAC)
Implement multi-signature authorization
Regularly audit permission structures
4. Flash Loan Exploits
The Issue
Attackers borrow large amounts of capital instantly and manipulate protocol logic within a single transaction.
Impact
Price oracle manipulation
Liquidity pool draining
Governance attacks
Mitigation
Use time-weighted average price (TWAP) oracles
Add transaction limits and circuit breakers
Validate economic assumptions
5. Oracle Manipulation
The Issue
Smart contracts rely on external data feeds that can be manipulated.
Impact
Incorrect pricing
Liquidation exploits
Financial loss
Mitigation
Use decentralized oracle networks
Aggregate multiple data sources
Implement sanity checks
6. Front-Running and MEV Attacks
The Issue
Transactions are visible in the mempool before execution, allowing attackers to reorder or insert transactions.
Impact
Arbitrage exploitation
User losses
Market manipulation
Mitigation
Use commit-reveal schemes
Implement private transaction relays
Design MEV-resistant protocols
7. Denial of Service (DoS)
The Issue
Attackers block contract functionality by exhausting gas or exploiting logic flaws.
Impact
Frozen funds
Unusable contracts
System downtime
Mitigation
Avoid unbounded loops
Optimize gas usage
Design fail-safe mechanisms
8. Unchecked External Calls
The Issue
Contracts assume external calls succeed without verification.
Impact
Silent failures
Broken logic flows
Exploitable inconsistencies
Mitigation
Always check return values
Use
try/catchpatternsValidate external interactions
9. Delegatecall Injection
The Issue
Using delegatecall improperly can allow attackers to execute malicious code in the contract’s context.
Impact
Storage corruption
Full contract compromise
Mitigation
Restrict delegatecall usage
Use trusted libraries only
Apply strict upgrade patterns
10. Upgradeability Risks
The Issue
Proxy contracts introduce complexity and potential attack vectors.
Impact
Unauthorized upgrades
Logic replacement attacks
Mitigation
Use secure proxy patterns (e.g., UUPS, Transparent Proxy)
Implement governance controls
Audit upgrade mechanisms
11. Logic and Business Model Flaws
The Issue
Even if code is technically correct, flawed economic design can be exploited.
Impact
Incentive misalignment
Protocol draining
Governance abuse
Mitigation
Conduct economic audits
Simulate attack scenarios
Stress-test tokenomics
12. Signature Replay Attacks
The Issue
Signed messages can be reused across transactions if not properly protected.
Impact
Unauthorized transactions
Asset theft
Mitigation
Use nonces and timestamps
Implement domain separation (EIP-712)
Validate signatures carefully
Emerging Risks in 2026
Smart contract security is evolving beyond traditional vulnerabilities.
Cross-Chain Exploits
Bridges and interoperability layers introduce new risks.
AI-Assisted Attacks
Automated systems can scan and exploit vulnerabilities at scale.
Composability Risks
Protocols interacting with each other increase systemic exposure.
Best Practices for 2026
To build secure smart contracts, teams should adopt a defense-in-depth strategy:
Multiple independent audits
Formal verification for critical logic
Continuous monitoring and alert systems
Bug bounty programs
On-chain anomaly detection
Gradual rollout and testing phases
Security is no longer a one-time process—it is a continuous lifecycle.
Conclusion
Smart contract vulnerabilities are not just technical flaws—they are systemic risks that combine code, economics, and infrastructure. As Web3 ecosystems scale, attackers are becoming more sophisticated, leveraging automation, financial engineering, and cross-protocol strategies.
The future of blockchain security lies in:
proactive design
layered defenses
real-time monitoring
and continuous improvement
Teams that treat security as a core product feature—not an afterthought—will be the ones that build resilient, trustworthy decentralized systems in 2026 and beyond.